Over the past week there has been a bunch of buzz about what essentially are Facebook marketing hacks; quick “guerilla” tactics that help boost exposure to your profile or brand. Whether you are a small business or a big business, there are some quick “tricks” that can instantly gain you more exposure. These Facebook marketing hacks are not encouraged by Facebook and ultimately, I would assume that Facebook will develop filters for people gaming the system.
Facebook Marketing Hack 1: Tag Popular Friends in Photos
This trick has been written about extensively over the past week. This Facebook hack is pretty straight forward. You simply upload a photo which has some sort of promotional value in addition to a photo description which can be used for promotional purposes. Proceed to tag your most influential friends (friends with the most contacts), and submit the photo.
Facebook places a high priority on photo tagging when it comes to news feed stories so this is a great way for getting promotion. As I said before, this is gaming the system though and Facebook will inevitably develop tools to monitor this type of activity. If you abuse Facebook tagging, you may not only begin to receive warnings from Facebook that your Facebook account will be deactivated, but you could also anger your friends.
Facebook Marketing Hack 2: Switch Your Relationship Status Regularly
This has to be one of the more aggressive hacks that I’ve found. Remember, I’m not necessarily endorsing these tactics, I’m simply exposing the various Facebook hacks that exist. You’ve probably noticed that every time one of your friends gets out of a relationship, or decides to seal the deal you end up getting a notification in your newsfeed about their relationship change.
That’s because Facebook places a high priority on relationship changes. These tend to be one of the less frequent activities within user profiles and as such they are prioritized to display whenever they take place. So if you are really aggressive about promoting yourself, go switch your relationship status and enjoy the countless clicks to your profile.
If you decide to go this route, you may want to have a promotional story published within your personal feed so that visitors arriving at your profile have other content to interact with.
Facebook Marketing Hack 3: Join As Many Events as Possible
Facebook events receive a high priority for the news feed, especially when multiple people within a given network of friends RSVP to attend. The more events you RSVP to the better and eventually your friends will begin receiving notifications that you’ve RSVPed and will also join. This is a secondary Facebook marketing hack as individuals are not directly driven to your profile but instead another event.
You are acting as a resource for your friends when you RSVP though and ultimately, the more often they see events that you’ve RSVPed to, the more often they’ll think of you as an event resource. This is a basic marketing strategy but it’s one that works. Some people are extremely aggressive with this and RSVP to every event regardless of whether or not they’ll be attending.
The end result is that people see you attending the event and occasionally click through to your profile, in turn increasing your exposure. It’s indirect marketing, but it works.
Facebook Marketing Hack 4: Import Blog Posts and Tag Friends in Notes
If you are trying to promote a brand or your own company and you have a blog, Facebook Notes should be your best friend. Facebook currently enables users to import one RSS feed from a blog or general news site and then each of those articles are published as Facebook notes automatically. To edit your settings go to the
notes settings page.
Don’t stop at just configuring your notes to import a feed though. Once you make a post and it’s imported to Facebook, head on over to that note and tag influential friends in that article. I’ve seen this work regularly and if friends comment on the article, it increases the odds that the note will show up in the news feed. Don’t over use this though!
If you start tagging friends in articles regularly, you are going to experience diminishing returns. First of all you’ll turn into the boy that cried wolf in that your friends will stop checking everytime they are tagged in a note. Additionally, Facebook could start ranking your notes lower for the news feed.
Facebook Marketing Hack 5: Wish Everybody a Happy Birthday!
This is less of a hack and more of a good activity to get in the habit of. Whether or not you are using Facebook to do this, you should be wishing everybody you know a happy birthday. Facebook has done most of the work for you, by tracking all of your contacts’ birthdays, they even recently added
birthday email notifications.
If you aren’t into wishing people a happy birthday just to be a good friend, there is also the promotional side of doing so. Wall posts are also optimized to show up in users’ Facebook news feeds. That means not only do you get to wish someone a happy birthday but there is also a chance that other people will see it!
Talk about a worthwhile activity! You get to build your relationship as well as promote yourself or your company. Personally, I also like to send my close friends a text message, a call, or take them out for a drink, but posting a Facebook wall post also can never hurt!
Facebook Marketing Hack 6: Engage in Many Poke Wars
Personally, I’m not one for poking often. With girls it tens to be more of a way to flirt or say “Hi!”, whereas with guys it’s a way to get their attention. Whatever reason you are using it for, it’s a good idea to poke more often. Why? Well it gets more people checking you out and it also may result in more promotional activities such as wall posts and other actions.
Make sure not to make people annoyed though. Ultimately, even annoying them can be good because it incentivizes them to take a public action. Alternatively they could remove you as a friend! This requires that you know when to stop but I’ll assume that you have basic personal communication skills and can figure that part out.
Facebook Marketing Hack 7: Switch Your Birthday Regularly
This is a pretty dirty tactic and I personally have never employed this one. Given that there are many other people that take advantage of the birthday notifications, you can get a fair amount of attention by switching your birth date around. This is flat out misleading people that don’t know you well though and probably not the best tactic to use with them.
This article isn’t about what’s right though, it’s about how to get people’s attention and build buzz for yourself or for your company. This is definitely one way to do it. Honestly, I don’t think that misleading your friends or potential customers is the best way to build buzz, but I’ll leave that decision up to you.
Facebook Marketing Hack 8: Re-Post Fan Pages Previously Created
Creating pages is a must do for any business. If you don’t know about Facebook Pages, go
check them out. This list isn’t everything about Facebook marketing, simply what the top 10 best Facebook marketing hacks are. Once you know how to create a page and get people registered, you should experience an initial surge (if you’ve done things right).
Following that initial surge there tends to be a lull and many struggle to make it through that lull and the Facebook Page tends to die off. There are a number of ways to get through this lull. The first one (and the one Facebook would like you to take advantage of) is Facebook ads. I’ve used Facebook Ads extremely well for one of my pages.
I highly recommend trying out Facebook Ads but there are a few free methods of promoting pages as well. The most effective tends to be reposting your page. As it happens, when you repost a page, you occasionally get the page reposted in friends’ news feeds. This is based on a number of factors that I can only guess about but, reposting one of the pages you want to attract new members to is never a bad idea.
Free Emails
Facebook Marketing Hack 9: Post Comments on Fast Growing Groups
This is a killer method and it’s one of the reasons that you see so much spam on Facebook walls. Fast growing groups as well as newly posted events with large guest lists are great targets for posting content. There are two types of things to post: relevant comments and links to pages. The reason for posting relevant comments is that it means you have something valuable to add to the conversation.
People tend to click on your profile if you add something valuable to the conversation. Extremely popular groups that are shooting for large memberships and have momentum are great places to place links to your site as well. I’ve seen links on these groups result in thousands of visits to a site. Personally, I don’t spend much time posting on walls but I’ve seen it work.
If you post a link on a group or an event, make sure the link is relevant as well. Posting irrelevant links may get you some traffic but the value of that traffic is substantially reduced when it’s not relevant. Additionally, Facebook could ban you for over posting links as it eventually crosses the line in to “spam”. Some groups even enable the posting of rich content. Post attachments with links to sites as often as you can if the events enable it. This will always drive quality traffic.
Facebook Marketing Hack 10: Mastering Facebook Event Marketing
Events are one of the best platforms for marketing on Facebook. I would go so far as to suggest that the Facebook events application has transformed the event industry. You can start an event and if properly promoted hundreds or thousands of people will end up registering for the event as it’s virally distributed throughout the social graph.
Invite Influencers
The first step in mastering marketing via Facebook events is to attract the most influential people to your event. Honestly, most promotion on Facebook involves the influencers, or central nodes in our social graph as their news feed “stories” tend to have the broadest reach.
Get Attractive People
I have never seen events explode like the ones that have a ton of attractive people registered to attend. Whether you like it or not, attractive people are called “attractive” for a reason. They will draw tons of people to your event. One of the first things people do when they view an event is check out the guest list.
If the event is all guys nobody wants to go. This is basic party promotion tactics and you should be using them on Facebook even for professional events!
The Power of Maybe
One last important component of Facebook events is that when you invite all your friends to them, and other people invite their friends, you can message all attendees even if they haven’t RSVPed. Unless a user comes and specifically enters that they will not be attending, they will receive your messages.
Facebook Marketing Hack 11: Import Your Email Contacts Into Facebook
This is one of the most simple ways for instantly boosting your contacts on Facebook. Frequently we forget who all of our contacts are so thankfully, Facebook has simplified the process for seeking out existing contacts. On Facebook’s
find friends page, there is the option to enter your email address and Facebook will automatically import those contacts to see which ones are already registered for Facebook.
In addition to displaying which direct email contacts you aren’t connected on Facebook to yet, the service updates Facebook’s database with other potential contacts you might know. As such, you don’t need to add everyone as a friend to receive a benefit from importing your email. One other trick is to import external email lists into your gmail (or email provider of your choice) contacts and then import those contacts into Facebook.
You can use this model to discover a variety of new contacts that may only be a degree or two away from you. Given that one of the keys of Facebook marketing is to have a large network of contacts, the Facebook contact import feature will help you jump ahead rapidly in your quest to master Facebook marketing.
Facebook Marketing Hack 12: Sync Your Twitter With Facebook
Many people prefer not to use Twitter but those that do, have rapidly realized the potential marketing power of Twitter. If you have a large number of followers you also begin to realize the power of using your social network as a resource. No matter where you are in your Twitter experience, linking your Twitter to Facebook makes it easier to keep everybody in your network up to date on your latest happenings.
The more that you update your status, the more likely that your friends will take notice of you on Facebook. This builds your contacts’ awareness of your activities and if properly leveraged it can also boost traffic to your company’s website. I choose to automatically post each article that I write directly to Twitter. This is not for everybody as some people are concerned about overloading their contacts with information and scaring them off.
Personally, I’ve had a net increase in followers by posting about my articles so I don’t feel too guilty about doing this. For those that vow never to get one Twitter, you can still update your status regularly, as it will have similar results. If you aren’t against Twitter, then simply install the
Twitter Facebook application and get your status and Twitter account synced.
Conclusion
After reading through the top 12 Facebook marketing hacks you may be thinking a few things. First, this is a lot of things to keep track of. If you thought that, you’d be right. Leveraging Facebook for promotional purposes is a pretty challenging task, even for those knowledgeable about implementing some of these hacks effectively. The bottom line is it takes time and it takes consistency.
The second thing you were possibly thing is, “Isn’t this spam?” Well, some of these hacks can most definitely cross the line into spam while others are not as aggressive. I’d imagine that you are smart enough to determine which of these should be done regularly, which should be done occasionally, and which should not be done at all.
Everything in Moderation
As such, make sure that you leverage these marketing tactics and others in moderation. Marketing in excess is called spam and spamming on Facebook is something you should avoid. Not only will you piss people off, but you also risk getting banned from the site completely.
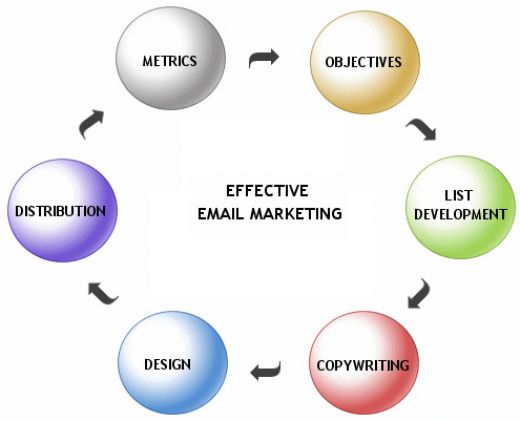
Build Your Network BY Email Marketing And Invite !
Click Here to get These EMAILS - Free EMAILS
One of the best ways to build your promotional abilities is by building your network. If you are one of the nodes in a network, there’s a good chance that your stories will receive a greater priority among your friends. So spend time adding your friends. One quick way to do this is to use the email address import tool found on the
Facebook invite page.
Often times you will instantly find hundreds of people that you’ve never connected with.
Say Hello!
It’s easy to rapidly turn into a robot once you start leveraging some of the Facebook marketing hacks outlined in this article. That is exactly when you need to take a break and say hello to new people. Did new people join your Fan page? Say “Hello!” and add them as a friend. Find out more about them. It’s important that you socialize with others rather than just promote.
Define Your Own Goals
Some people just want to self promote themselves while others want to promote their business. Whatever you are trying to market, Facebook can help you accomplish your goals as long as you know what they are. If you stay consistent with your Facebook marketing activities, you will soon accomplish your goals.